Documentation Index
Fetch the complete documentation index at: https://docs.tight.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Tight integrates directly with Google Cloud Storage to periodically upload raw accounting data to your own GCS buckets. By pushing data into your GCS infrastructure, Tight eliminates the need for your data team to build direct connections to the Tight API, allowing your team to work in the data stack they’re already using. Data is exported in Parquet file format on daily, weekly, or monthly intervals, including bank linkage data, invoices, lifecycle events, and transactions. Learn more about available data types and use cases in the Data Lakes guide.Create a Service Account
First, create a service account to grant programmatic access to the Google Cloud Storage bucket. In the Google Cloud Console, navigate to IAM & Admin → Service Accounts and click “Create Service Account”. Provide a descriptive name like “tight-api-data-access” and description: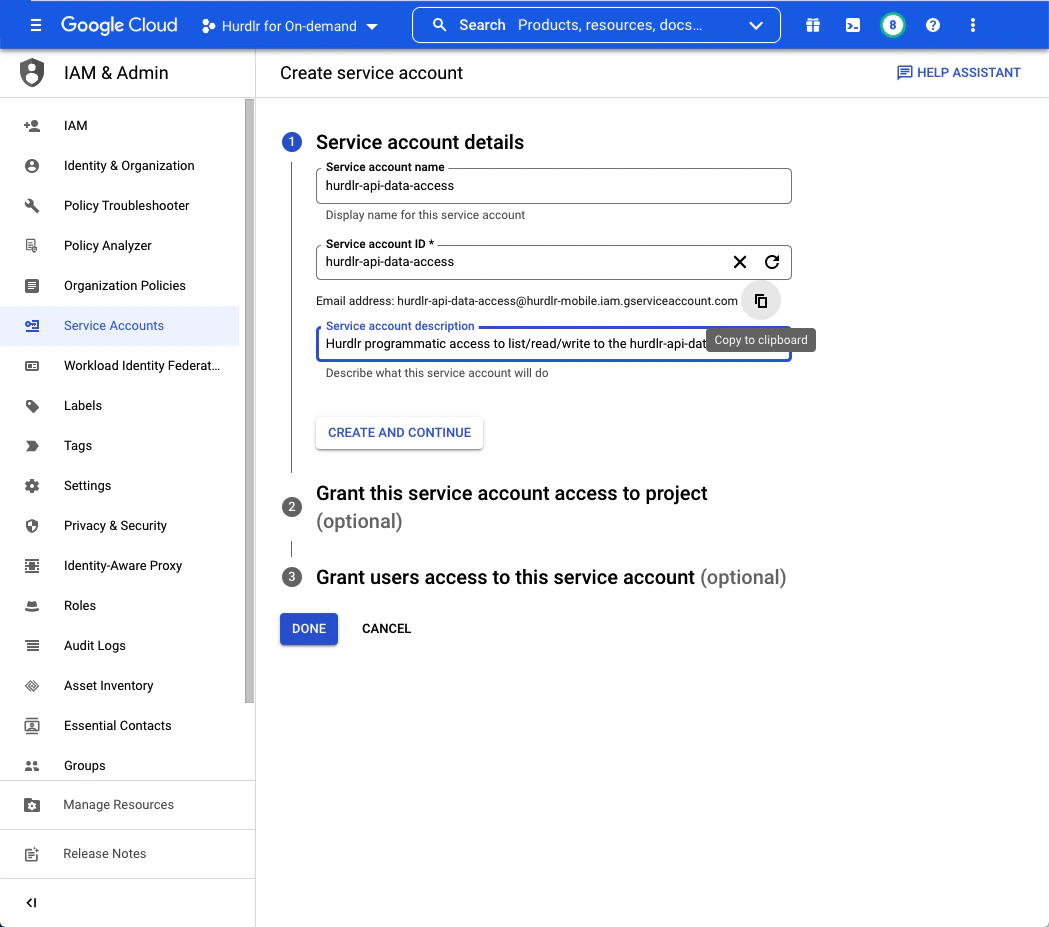
Create a Google Cloud Storage Bucket
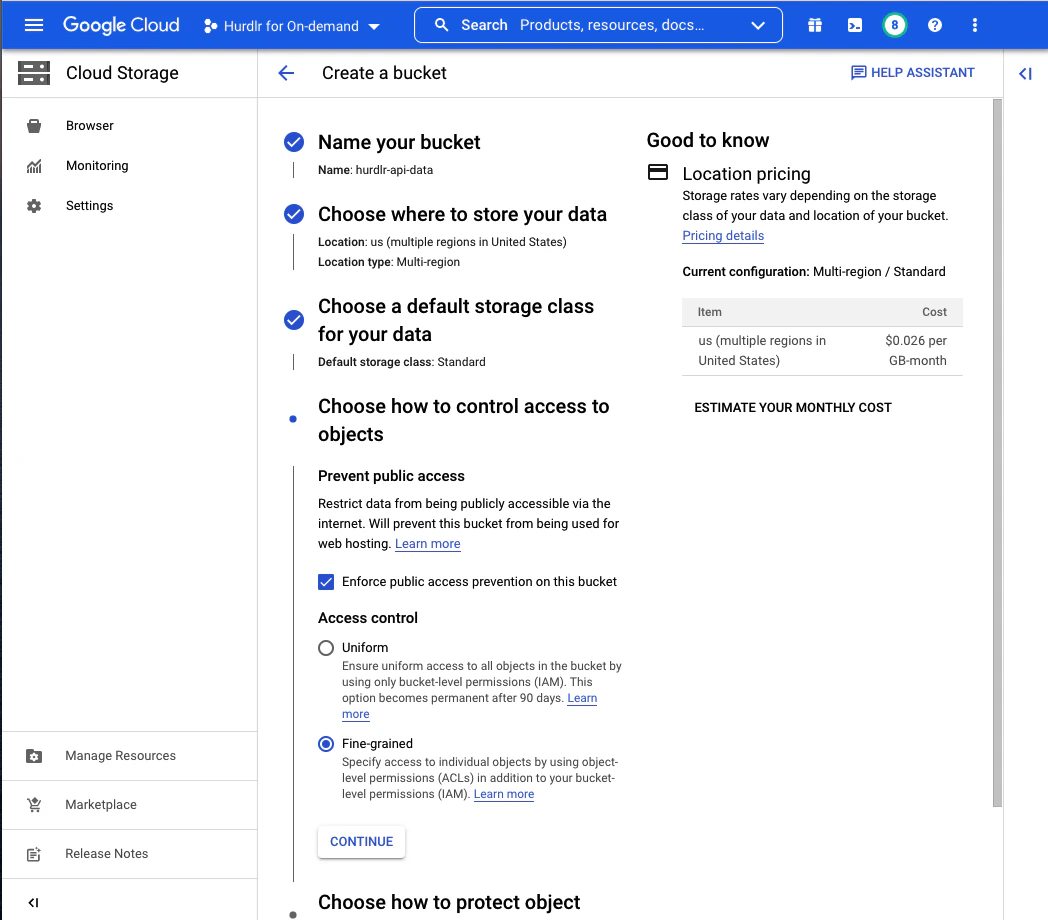
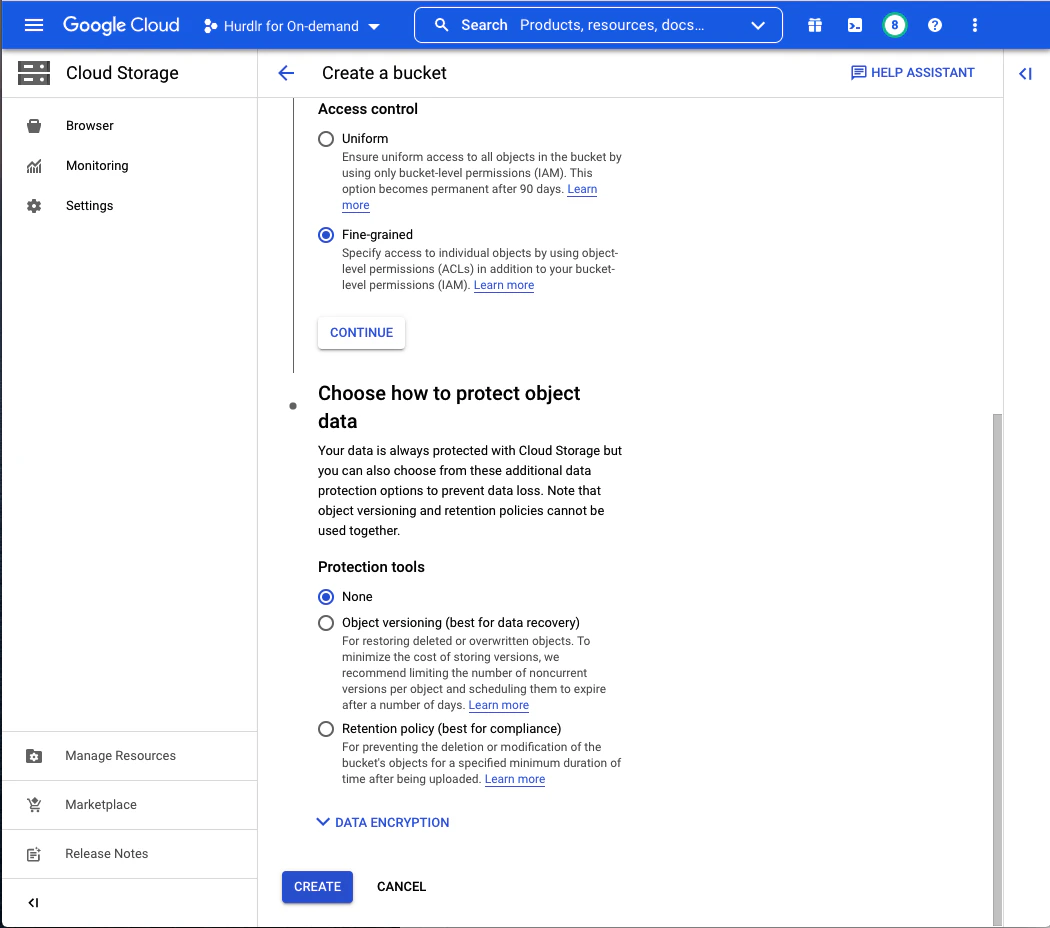
Next, create a Google Cloud Storage bucket where Tight will store your data. We recommend naming this bucket “tight-api-data”: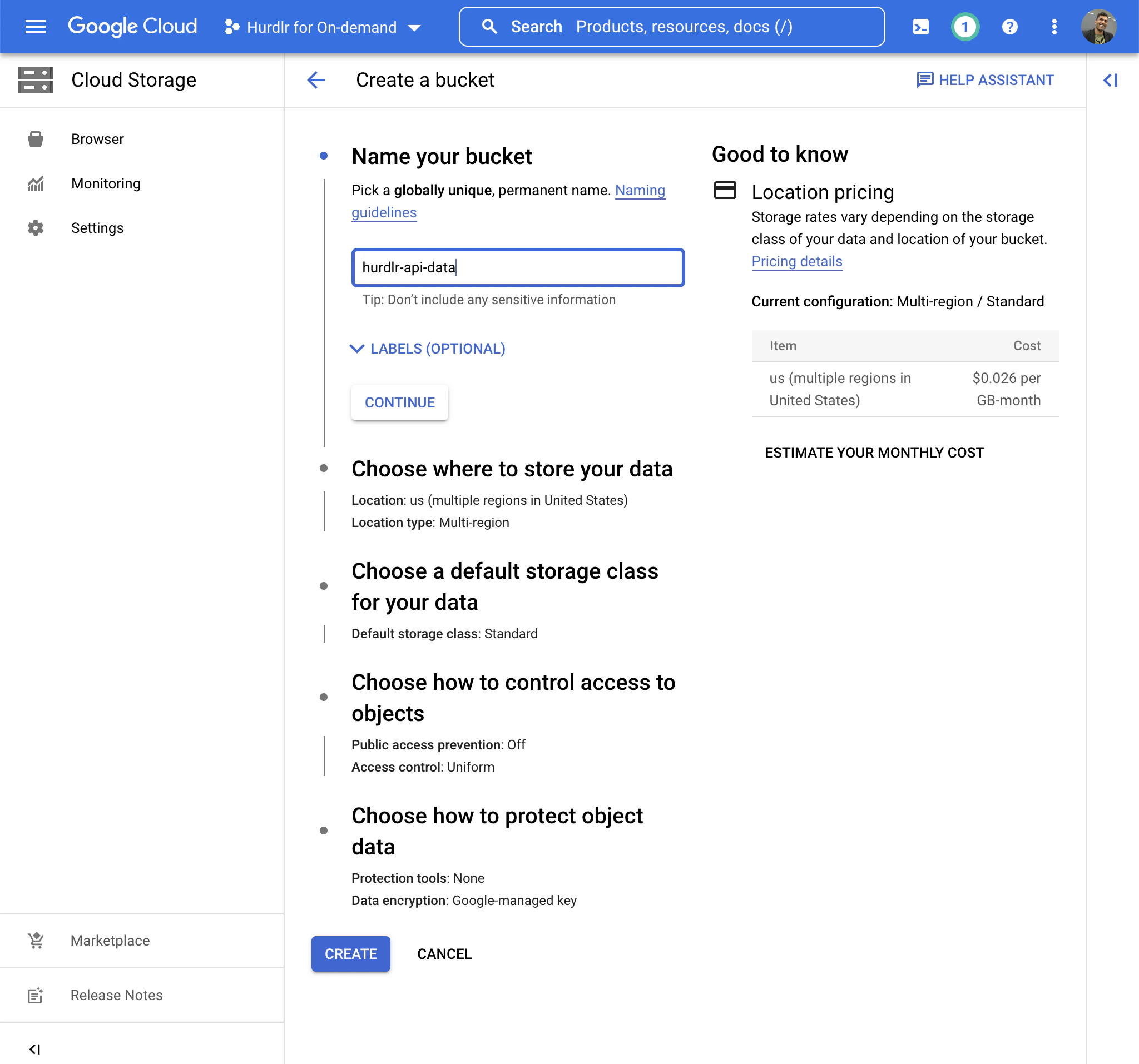
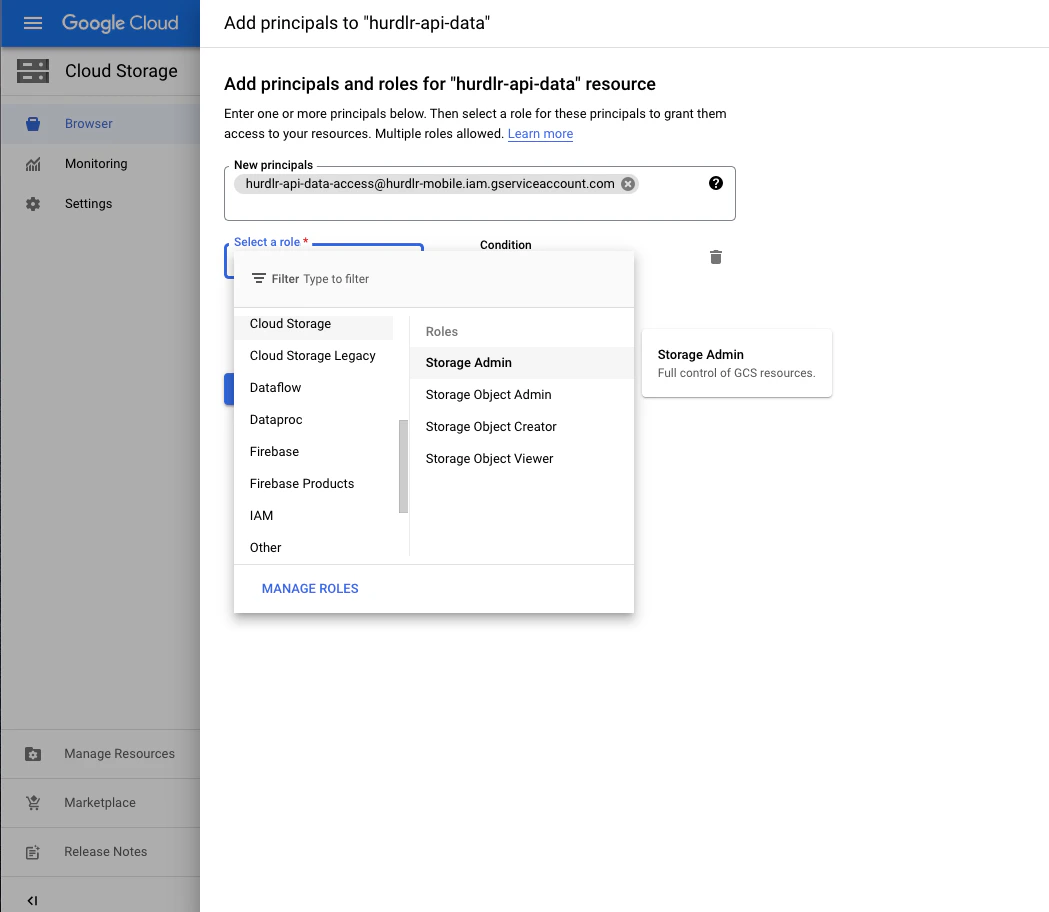
Grant Service Account Access to Bucket
Once the bucket is created, you’ll be taken to the Bucket Details screen. Click on the “PERMISSIONS” tab and then click “ADD”: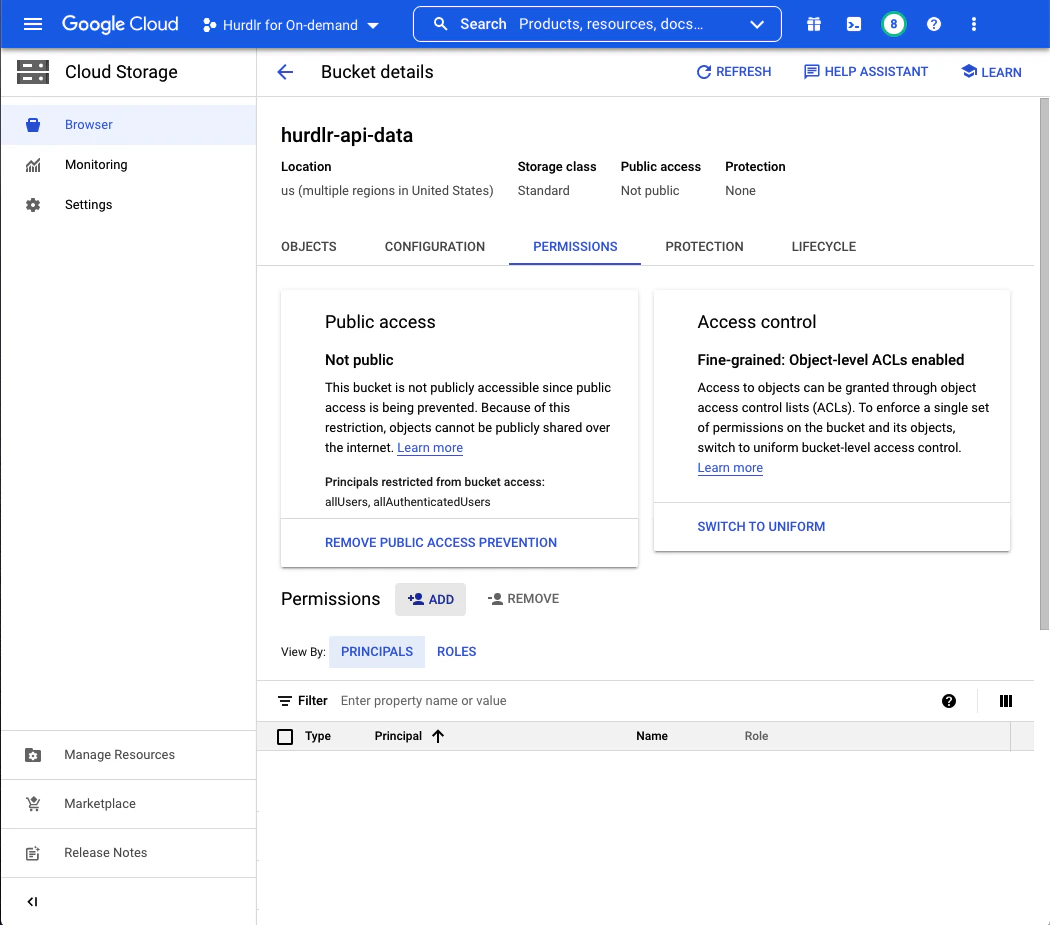
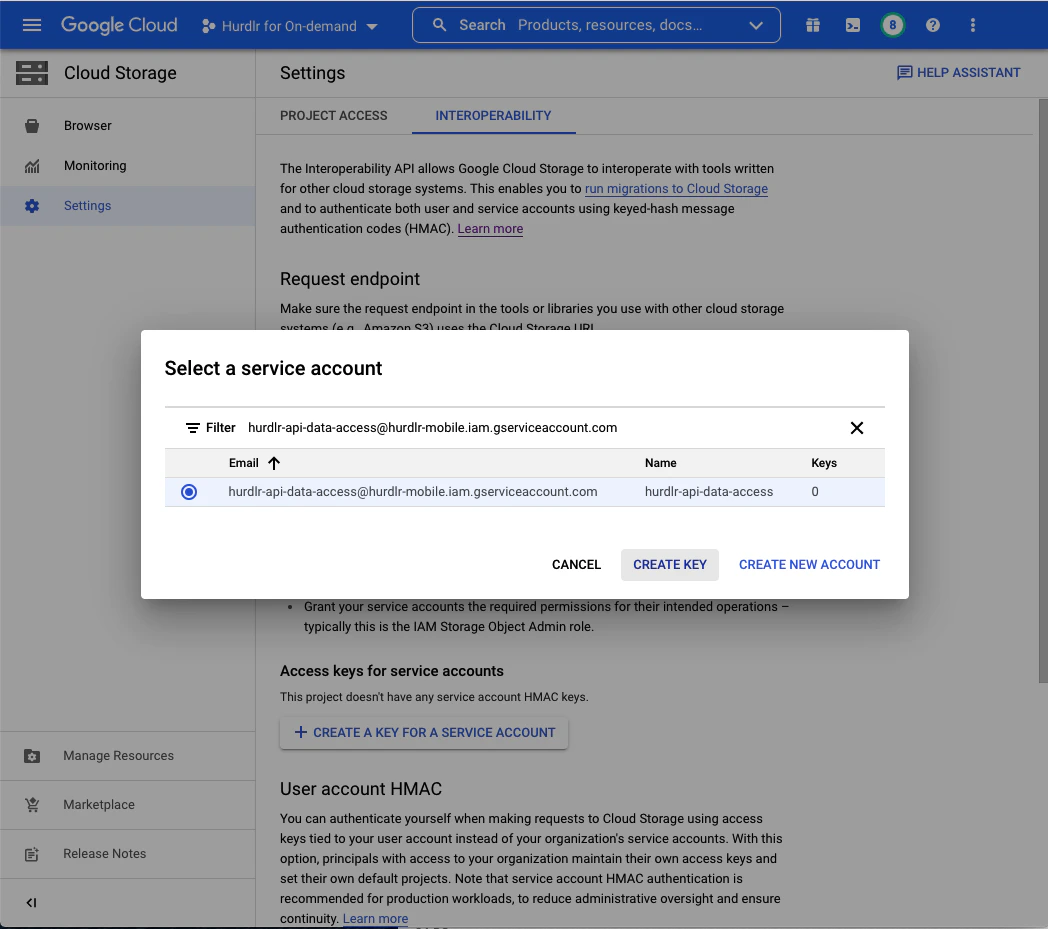
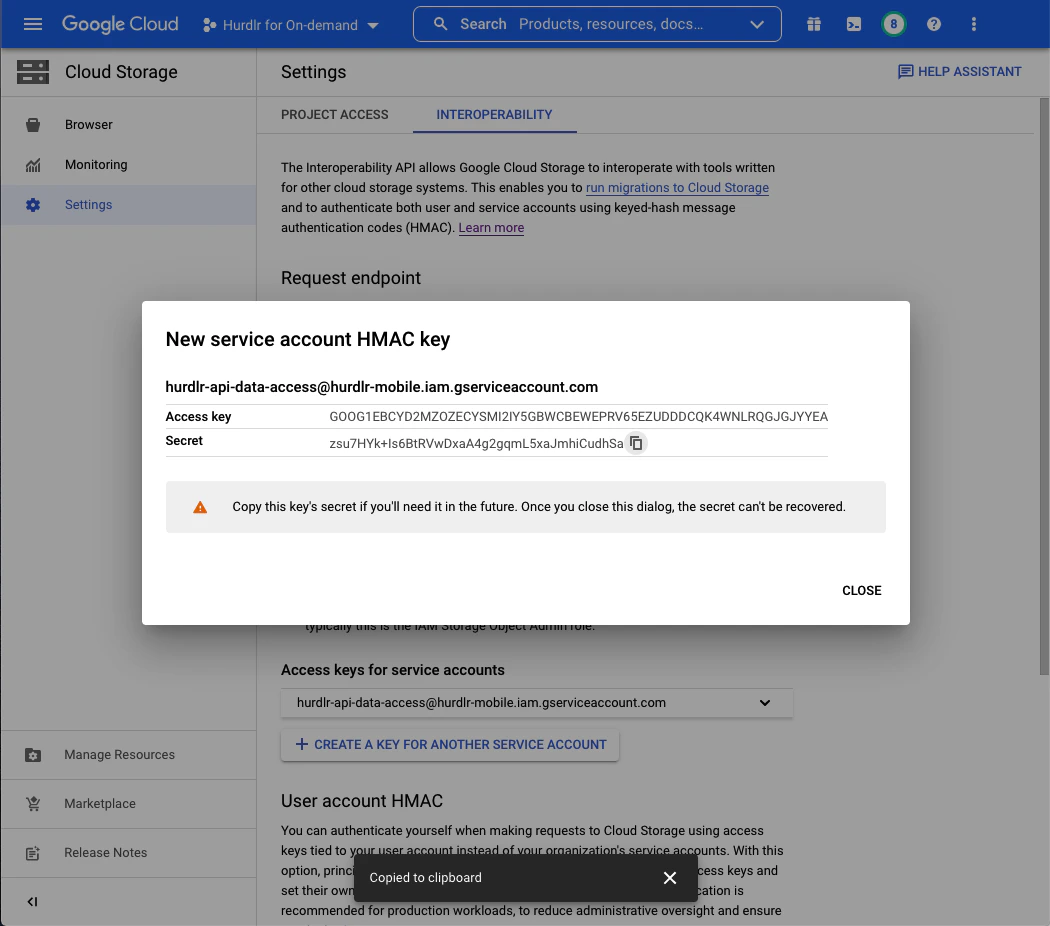
Create Service Account HMAC Key
Next, create a service account HMAC key for authentication. From the Cloud Storage screen, click on “Settings”, then select the “Interoperability” tab: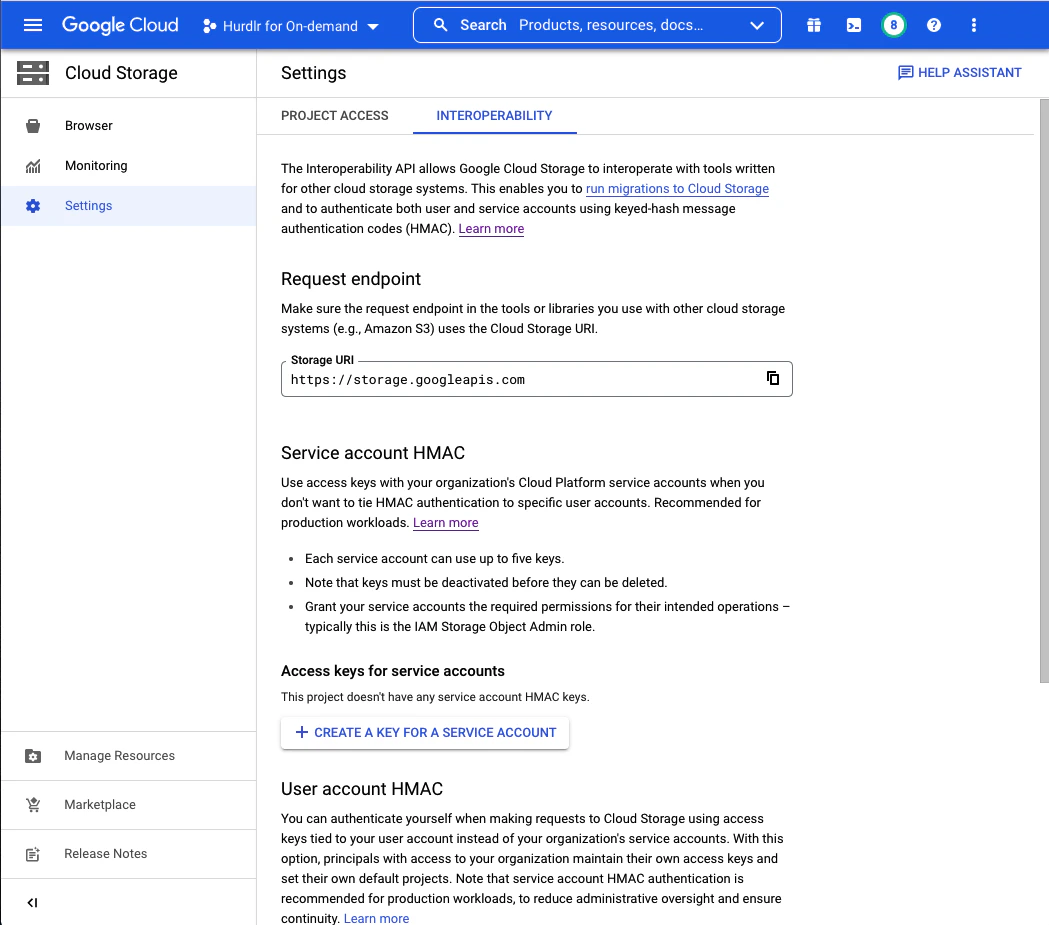
Securely Share Access with Tight
Contact Tight directly at api@tight.com for instructions on how to securely share:- Your GCS bucket name
- The HMAC Access Key
- The HMAC Secret